In this episode I’ll talk about an Outlook Addin from Microsoft that helps you to improve and optimize the detection rate for Fale/Positives.
For example, if a mail was classified as junk, you can report this mail as normal mail and it will be moved to your inbox. The same the other way round: If a Junk mail ends up in your inbox, you can report it as Junk or Phishing.
This way Exchange Online Protection learns for you and evaluates the mails accordingly in the future.
iOS accounts needs permission to access Office 365 resources
If you followed the security recomendations in Office 365 and disabled the ability for users to consent for apps, iPhone users will be facing the message “iOS accounts needs permission to access resources in your organization” during native mail account setup for Exchange Online.
I had this situation and find some articles to solve the problem. I would like to give you a short summary of these articels.
Continue reading “iOS accounts needs permission to access Office 365 resources”Manage Microsoft Exchange Online when using AAD Connect
Few weeks ago I had to implement Microsoft Exchange Online for a customer who didn’t used Exchange in the past. For a simple user management, I decided to install and configure Azure AD Connect. So the user accounts from local Active Directory will be synchronized to Azure AD.
There are several advantages of this scenario:
- you have a single point for user management, your local Active Directory
- if configured, user passwords (or better to say password hash values) are automatically synchronized to Azure AD
- the user has a Single-Sign-On Experience for Office 365 services
- Office 365 license assignment based on local AD groups
After setting up Azure AD Connect and enabling all users for Exchange Online, I started to configure some Exchange settings: configure distribution lists, shared mailboxes and second mail addresses. But wait, what’s that? After submitting the change and error message pops-up:
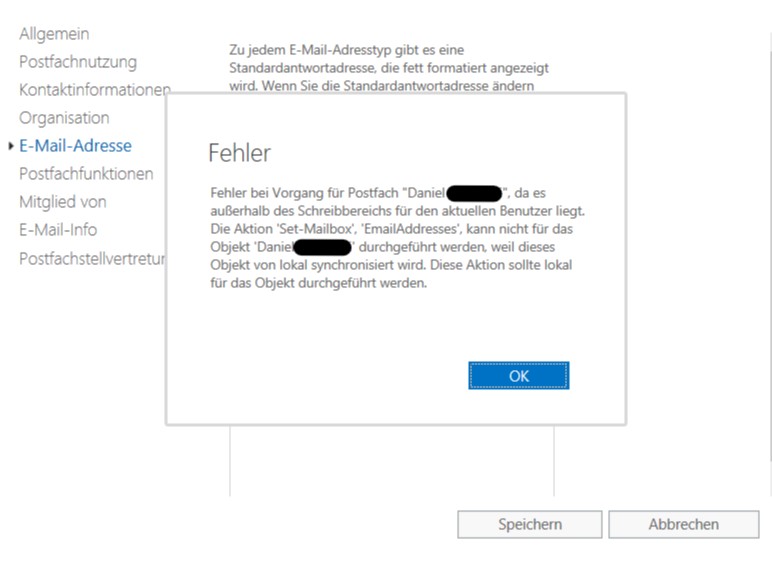
What da hack? After some research in the web and reading several blog entries, it was clear: When using AAD Connect and synchronized accounts in Office 365, you have to install an on-premises Exchange Management server for changing some Exchange Online settings. Even you don’t have an on-premises Exchange server installed yet. Very disappointing and frustating. That’s why a customer decides to use cloud service: they wan’t have to install and maintain the system on-premises.
Continue reading “Manage Microsoft Exchange Online when using AAD Connect”